Vulnerability & risk scans
For optimum cyber security, availability and compliance
There are two kind of vulnerability and risk scans: organizational and technical.
The organizational part is about threats and risks around business continuity; part of which is a recovery plan, security incidents and their response processes. The technical part is related to the supporting activities like backup and disaster recovery, automated vulnerability scans and pen-testing.
With this in mind we work with 3 type of vulnerability and risk scans:
-
-
- Essential
- Standard
- ZeroRisk
-
All scans are available as a one-off and customer friendly, flexible subscriptions. Where subscriptions vary from a guided DIY (i.e. Do IT Youself) to a full managed service.
The Essential scans investigate which doors are open and the chances of a “successful” burglary. We do this by knocking digitally at every door. If there is an answer, we ask who is present and what function everyone has.
Expressed in technical terms: via an automated scan we test all 65535 TCP ports for establishing a connection. If this is successful, the device is queried for software functions and version numbers.
In addition, the chance of success with a targeted attack is examined. We do this by researching things with the hacker perspective into:
- Access to the company website via DNS and certificates.
- Easy to execute attack scenarios; for example with fake invoices.
- Publicly available personal and company information.
The aim of this part of the research is to determine to what extent visitors and e-mail can easily be redirected to a rogue website and dito mail server.
With the Standard scans, the Essential scans are completed with the following options:
- Relevant Essential scans are now also executed on the internal network.
- Advanced Black/Grey/White-box pentest scenario’s (where needed).
- Map and scan of all inbound and outbound network/application traffic.
The purpose of the Standard scans is providing insight into the digital footprint of an organization; including available personal and company data should an intruder gain access through one of the user accounts.
The ZeroRisk scans take the Standard scans as a starting point. This is complemented by organizational aspects.
The goal is identifying low-hanging fruit based on relevant governance frameworks like BIO (Dutch), NIS2, ISO27001 and GDPR. This includes things like:
- social engineering,
- various forms of access controls and
- disaster recovery plans.
Afterwards you know where your vulnerabilities and risks are; both organizational and technically. This can be made more tangible by running our Cyber Crisis Simulation.
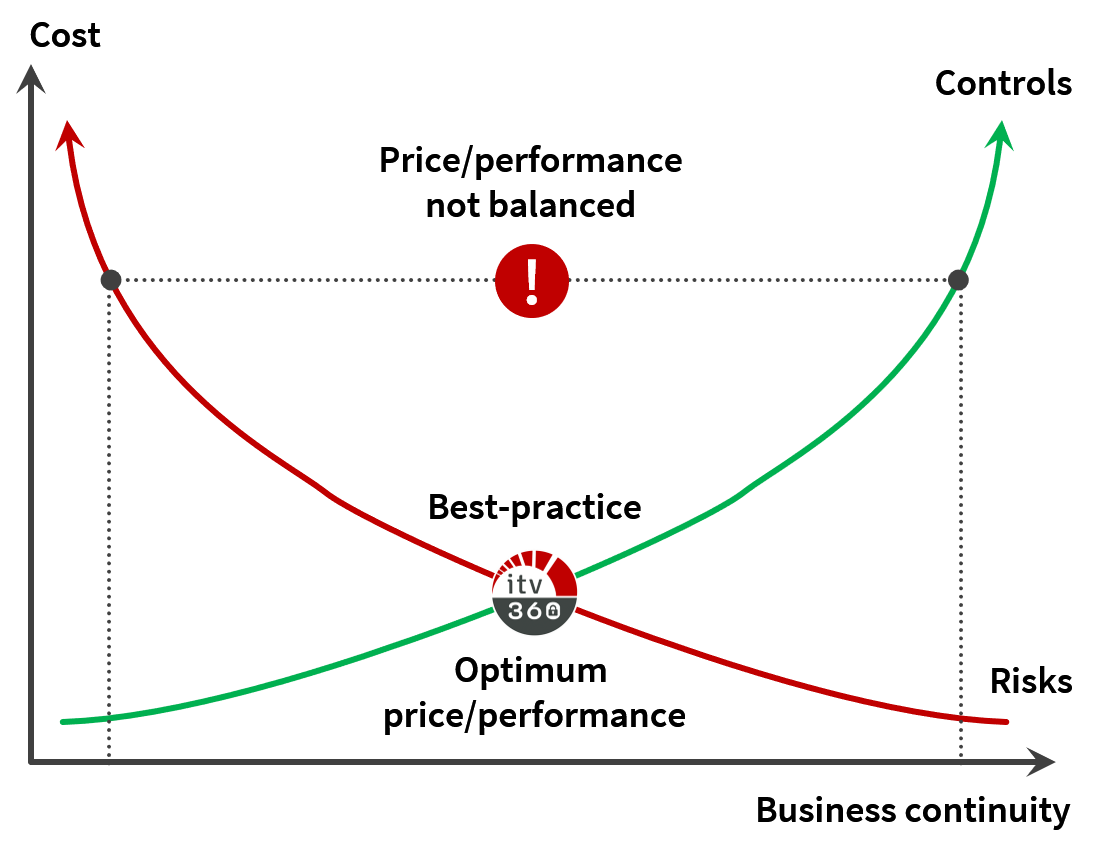
A more then essential part of a safe, digital workplace with a healthy balance between risks and controls.
Interested?
Contact us and we are happy to explain how we work.