End-to-end ZeroRisk IT and applications
Application resilience starts with the end-user
Most organizations already made significant investments in incident response processes and accompanied monitoring systems:
- Assure any given user has his or her unique digital identity; typically based on Active Directorybased on Directory-as-a-Service.
- Event-based SIEM systems tracking security related content of log files.
- NextGen Intrusion Detection/Prevention System (i.e. an IDS/IPS) to detect and remove suspicious behavior of application traffic.
If everything fails there is always a backup ready; combined with a disaster recovery procedure. Since both are part of a GRC-process that proofs everything is working as expected.
But what about the user behavior across all those applications and IT layers? How do you know which users and devices are trying to get access? Where do you start when being “ransomized”? How do you know that the backup you need to restore is not affected?
If these things are your main concern, then let’s have a chat and learn how we help with our end-to-end ZeroRisk approach!
Vulnerability scan
Any resilience and integrity approach starts with a thorough vulnerability scan:
- Detect well-known vulnerabilities on endpoints, webapplications and network devices.
- Detect all possible network connectivity
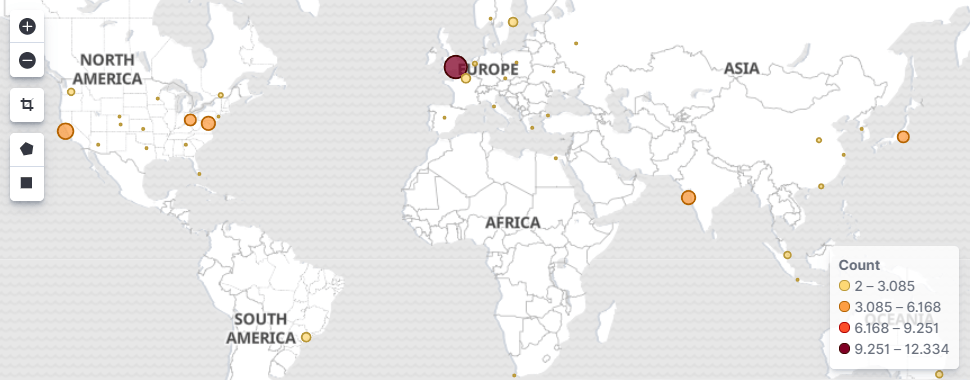
- Realtime detection of all active network connections, their respective endpoints, geo-location and service.
The results are screened based on a end-to-end ZeroRisk policy. This policy reflects the risk appetite of your organization.
The outcome is an ISO27001 and PCI type of management summary. This is completed with a detailed, hands-on set of recommendations.
Multi-factor Authentication based Directory-as-a-Service
Directory-as-a–Service and Multi-factor Authentication (from here-on called DaaS and MFA) are the foundation for user and device authentication. You could think of it as the safe-guard for weak passwords and unsafe devices. Meaning logins are only allowed from pre-defined, trusted locations and devices; assuring any malicious access attempt is stopped. As a site effect, it prevents identity theft.
In addition, this approach includes tracking the connection details based on internal and external IP-addresses. These connection details feeds other safe-guards like firewalls and the endpoint protection engine.
Endpoint protection
The endpoint protection engine only allows access to business applications coming from well-known, trusted IP-addresses and endpoints. On top of that, the engine baselines normal system operations. If any of this is not behaving as expected you will be alarmed. Optionally, whatever is misbehaving it will be stopped and blocked.
The outcome is a very effective and efficient way to maximize resilience and integrity of an endpoint, its applications and its data!
All this is working location and device in-depended. Meaning it doesn’t matter where the user is located and what device is used. In addition, Active Directory, SD-WAN and VPN’s are optional(!); *not* mandatory!
How this helps you and your organization
With our end-to-end ZeroRisk approach the chances for a security breach is close to zero. This is because any policy is enforced for any kind of user-to-machine connection as well as machine-to-machine connection; just as long as both are part of the Directory Service. If not… well… I guess there is a user and/or an endpoint into play that is not supposed to be their…
The next step
Learn how you and your organization can benefit from this. Prevent installing any kind of malware; let alone malware becoming ransomware!
Feel free to fill the form on the top-right of this page and we are happy to pay you a visit explaining things in more detail.