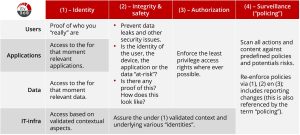
ZeroTrust ITV360: the 4 pillars of a ZeroRisk workspace
For optimum cyber safety, availability and compliance
Especially small(er) organizations are struggling with the ever-increasing demands on their IT and applications. This is because of the “anywhere, anytime, anyplace” type of requirements. Part of these requirements is cyber-safety and privacy related due to different legal regulations.
With our 4 pillar modular approach we will guide you in your ZeroTrust journey:
- End user
- Strong passwords
- Two/multi factor authentication
- Context: device and location
- Applications
- Least privilige access where possible
- Assure integrity & safety
- Data
- Least privilige access
- Limited data set where possible
- Assure integrity & safety
- IT infrastructure
- “keep it run like clockwork”
- Access based on predefined context
- End-to-end surveillance
- Scanning of actions and content
- Re-enforce context and identity
- Signalling and reporting
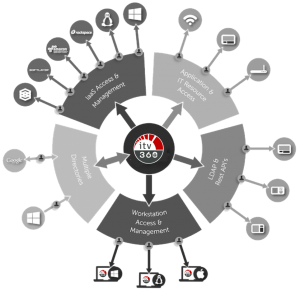
The 5 technologies for our ZeroTrust best practices.
These best-practices include re-using existing resources where possible!
Learn more
Fill in the form below and learn how we can guide you in your ZeroTrust journey!